SSL (Secure Sockets Layer) is the standard security technology for establishing an encrypted link between 2 devices for example your web browser and the site you are visiting. The SSL connection between the devices ensures that all data passed between them is encrypted and remains private, as SSL is an industry standard it is used by millions of devices and websites to protect data in transit (from your browser to the server). In modern systems they will now be using TLS (Transport Layer Security) which has replaced the traditional and deprecated SSL technolagie, most people still refer to TLS as SSL for example you dont oftern see a site selling TLS Certificates they still refer to them as SSL Certificates which is the widly accepted term even if it is using TLS.
How do I get a SSL certificate
The simplest way to obtain an SSL certificate for your site is to contact your web hosting company they will be able to offer you a certificate (if they sell them) or at the very least point you at where you can order one from, they should also be able to advise on the type of certificate that you would be best suited for your site, ultimatly the decision is your so it's always worth investigating yourself as you will know your requirements best.
How do I know the connection is secure
To be able to create a secure SSL connection a web server this will require a valid SSL Certificate. For the case of your website certificate the users browser provide them with somesort of indication the connection is secure, in most cases this shows a padlock in the address bar to indicate an encrypted SSL connection.
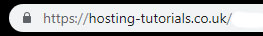
As you can see below when using Chrome this shows a padlock for the secure connection.
Not Useing SSL
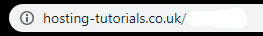
Using SSL